Hello,
I think that my database field may be invalid when my user is going to send request to my server.
For this, I have a basic question , can Json have a XSS bug when show’s or receive’s its data which has rendered to like json api? or Xss bug is just in HTML render ?
Thanks
Yes, there are potential XSS issues with JSON too. For one thing, if your client-side code uses the JSON contents to update the DOM, you might end up with a Client XSS vulnerability.
Also, some browsers have been known to be too “smart” about rendering contents in a user-friendly way, which has led to XSS issues. It is therefore recommended to set the “X-Content-Type-Options: nosniff” header in JSON responses. Even if your API is only intended to be used via AJAX, you need to protect users who might end up accidentally (or being tricked into) loading the JSON in a browser page.
Finally, you are talking about a database field being ‘invalid’. Remember the first rule of XSS prevention: don’t sanitize input (e.g. before inserting into your DB) but sanitize output. The exact escaping requirements depend on the output context, so the same DB field used in HTML, CSS or JSON would require different escaping. So the DB field cannot be inherently ‘invalid’, only the way you render it.
6 Likes
Can anyone create a bug in this page? I mean just this page (Json page) !!
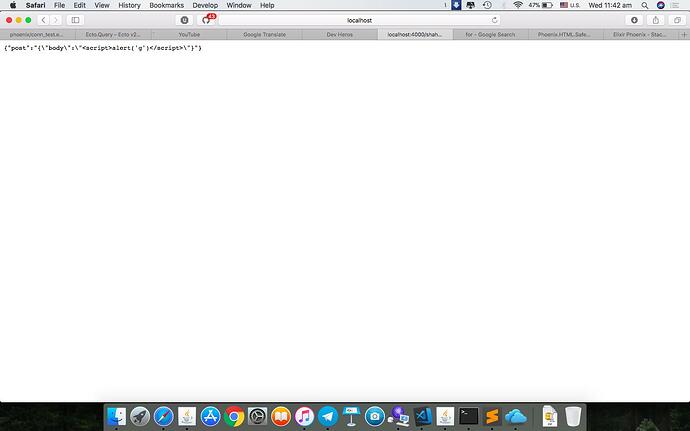
If your answer is yes ! for example how can I create programing document which <script>alert('g')</script> is in it? like the this answer
Assuming the Content-Type header is set correctly, loaded into a browser window like this it shouldn’t cause any issues, though as I said, it is recommended to set the nosniff response header to prevent browsers from interpreting the document as anything other than what the Content-Type indicates.
But if you were to consume this from client-side JavaScript and insert the value into the DOM using element.innerHTML= or document.write(), then the alert would probably get executed. This should be mitigated in the client-side code.
3 Likes