Hello @fhunleth
I’m using vintage_net_wifi version 0.12.1 which should have the changes you had mentioned in the above comment.
I’m trying to configure my device using the same method, however it is failing to connect to the network. Attaching logs for your reference
iex(19)> VintageNet.configure("wlan0", %{
...(19)> type: VintageNetWiFi,
...(19)> vintage_net_wifi: %{
...(19)> networks: [
...(19)> %{
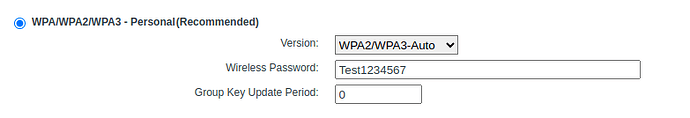
...(19)> ssid: "TestWifi",
...(19)> psk: "Test1234567",
...(19)> sae_password: "Test1234567",
...(19)> key_mgmt: [:wpa_psk, :sae, :wpa_psk_sha256],
...(19)> ieee80211w: 2
...(19)> }
...(19)> ]
...(19)> },
...(19)> ipv4: %{method: :dhcp}
...(19)> })
:ok
12:06:55.902 [info] RouteManager: clear_route wlan0
12:06:55.915 [warn] RouteManager: new set_connection_status wlan0 -> :disconnected (Elixir.VintageNet.Interface.start_configuri)
12:06:56.516 [info] wlcore: PHY firmware version: Rev 8.2.0.0.243
12:06:56.572 [info] wlcore: firmware booted (Rev 8.9.0.0.83)
12:06:56.600 [info] IPv6: ADDRCONF(NETDEV_UP): wlan0: link is not ready
iex(20)> ifconfig
lo: flags=[:up, :loopback, :running]
inet 127.0.0.1 netmask 255.0.0.0
inet ::1 netmask ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff
hwaddr 00:00:00:00:00:00
can0: flags=[]
can1: flags=[]
eth0: flags=[:up, :broadcast, :running, :multicast]
inet 192.168.0.100 netmask 255.255.255.0 broadcast 192.168.0.255
inet fe80::3684:e4ff:fe1e:8dac netmask ffff:ffff:ffff:ffff::
hwaddr 34:84:e4:1e:8d:ac
wwan0: flags=[:broadcast, :multicast]
hwaddr ce:c2:fb:b5:9e:43
wlan0: flags=[:up, :broadcast, :running, :multicast]
hwaddr 38:ab:41:4a:9a:f0
ppp0: flags=[:pointtopoint, :multicast]
12:07:05.574 [info] Start inverter init
iex(21)> VintageNet.get
get/1 get/2 get_by_prefix/1
get_configuration/1
iex(21)> VintageNet.get_configuration("wlan0")
%{
ipv4: %{method: :dhcp},
type: VintageNetWiFi,
vintage_net_wifi: %{
networks: [
%{
allowed_key_mgmt: [:wpa_psk, :sae, :wpa_psk_sha256],
ieee80211w: 2,
key_mgmt: :wpa_psk,
mode: :infrastructure,
psk: "F887CDC82262134FC3A3A8D458AF76BF2C0124FC62B915A61990F9AAA6533B6E",
sae_password: "Test1234567",
ssid: "TestWifi"
}
]
}
}
With same version if use below command it gets connected to the network
VintageNet.configure("wlan0", %{
type: VintageNetWiFi,
vintage_net_wifi: %{
networks: [
%{
key_mgmt: :wpa_psk,
psk: "Test1234567",
ssid: "TestWifi"
}
]
},
ipv4: %{method: :dhcp}
})