That’s so awesome, thanks for your work and commitment to causes like this!
Thank you. 
Thank you for your detailed questions and interest. I’m so happy to respond to your thoughts and concerns, and I think I can address them all  .
.
That’s my data
Yes, by asymmetrically encrypting your data on Metamorphic, I ensure that Metamorphic nor anyone but the person logging in each session with their correct password can decrypt their data and thus use it. In this case, using the data means on Metamorphic’s service to share with the people you choose to share with.
I also have an awesome future idea for how people can utilize the fact that they truly own their data on Metamorphic, to pay for the cost of their accounts even (and maybe make money) depending on the success of the service and if they choose to. But, I’m not saying more on this one yet, but it would still preserve and respect their privacy to some degree (though obviously less of a degree than before if participating it). It’s not set in stone, there’s a lot I have to think futher about and figure out, but I think there’s interesting options here to make the service more affordable for people and actually make their data work for them rather than against them. We’ll see.
I should note that I won’t do anything that I feel actually removes all or any of the protections I’ve worked so hard to put into place. It’s more that I’m just aware that some people may not be able to afford Metamorphic and I’m also trying to find ways to make it work both ways. 
US Big Tech
I’m changing the name of the cloud tech companies here, because it’s really essentially a conversation about the giant surveillance capitalists (Google, Facebook, Amazon, now Microsoft, possibly Apple (but they’re so private we don’t have the same level of evidence at this point)).
It’s hard to find anything in tech that’s not supported directly or indirectly by these players. In fact, almost all of the undersea cables are run by them (so your data is going through their infrastructure regardless). And along the way it’s being siphoned by the spy agencies (typically at the access points) either with direct or indirect cooperation by these same companies.
This is why strong encryption is so important (and maybe why Facebook is trying to find ways to work with encrypted data in their pipelines – this may be more marketing hype than reality but I don’t know any more yet about that). As Bruce Schneier wrote, encryption keeps you safe.
I need to also be fair to Big Tech, they contribute a lot of good things to. And lots of amazing and gifted people work for these companies. And it’s hard to not have to rely on them in some way or another. However, we could reorganize the private-public arrangement around technology and have a probably far more equitable and advanced space (but this is an entirely different discussion  ).
).
On Encryption
If you read Glen Greenwald’s book on the Snowden disclosures, you’ll see that even simple configuration changes can make the difference between whether or not the NSA can successfully get your data. That seems aligned with the nature of tech, if your program is designed for certain things and the data doesn’t match up then your program tends to not work as expected.
This suggests to me me that strong encryption really does provide some solid cover for both your privacy and your data. We use the NaCl/libsodium library for the asymmetric encryption because it needs to be as airtight as possible and that library is as good as it gets (as far as I know at this point), and makes it possible for me to utilize such strong encryption safely with such limited resources.
Yes, security is really all about the tradeoffs of time and money.
On the GDPR
This law is so important (as is the California law, Illinois biometrics law, and others) but they aren’t enough and don’t go far enough in actually addressing surveillance capitalism.
For instance, I know from personal anecdotes of people in the industry here in the U.S., that the GDPR effectively allows them to continue with business as usual. So, while it is important, it’s not enough and Facebook rendered it meaningless by swapping their legal structure to have everyone’s data be effectively domiciled outside the reach of the GDPR. So, it’s unfortunately not enough to protect people but is is an important and great first step.
On Payments
Thanks for sharing the PayPlug link. I haven’t had time to read through in any detail but I wasn’t aware of them prior.
This is a tough space for privacy, you may be able to use one of those Visa gift cards for Stripe but I haven’t tried it. If that works, then you could use that with an anonymous email through DuckDuckGo or other services and have some strong privacy on the payments front with Metamorphic. Again, I haven’t tried it so I don’t know if it will work but it seems plausible.
Stripe also has a great climate program that makes it very easy to automatically donate part of your payment straight to funding climate programs. For me, that was another important consideration.
On Social Media
One of the most important things about social media is that is has shifted the access to the public sphere into the digital space with the potential to democratize it and give everyone a voice. A healthy public sphere is essential to a healthy society. Long long ago, in a galaxy far far away… ( ) the public sphere was a physical public space or square and people could/would debate and share ideas on how to organize and govern their communities (this is a more democratic example).
) the public sphere was a physical public space or square and people could/would debate and share ideas on how to organize and govern their communities (this is a more democratic example).
With this idea, if you participated in the public sphere you agreed to give up some of your privacy in order to preserve trust and lend credibility to your opinion. It also meant you needed to think about how you conducted yourself and treated others because your friends and community members would know that their neighbor behaved such-and-such way, etc.
So, there is an important aspect to giving up some privacy when you agree to participate in the public sphere. And it’s important to note that this sacrificing of privacy is known by you, initiated by you, and under your control – and in return for your ability to meaningfully participate.
With Metamorphic, my first step and goal is to empower people to take back control over their digital lives and regain some of their privacy. This means all the steps I’ve taken to create a system like this. My second goal was to remove all of the dark pattern design that addicts you and really hurts your mental, emotional, and social well being. This means that Metamorphic is more than just a privacy-respecting clone, there are significant differences in the way you interact and use the service (which I hope will translate to people spending less time on it and more time with life). The next step is to enable the ability to participate in the public sphere but in a manner that leaves it up to you, under your control, and still with a level of protection not currently happening on the major platforms. These public sphere participation features are future features and I can’t say more about them at this point as they’re still very early ideas.
A lot of the harmful stuff that happens on major platforms, are already rendered moot on Metamorphic by nature of its design. But, there are still lots of other things that I have to think about and consider as I develop Metamorphic.
Book worth reading: The Social Construction of Reality
Early Access
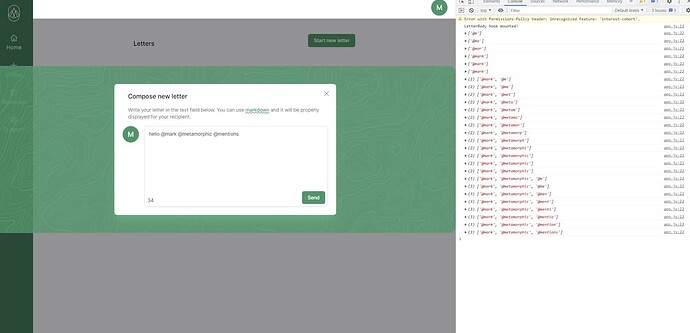
With early access, you sign up with an email address. This email address is symmetrically encrypted. When you get invite codes, you can then create an account at which point your account data is immediately asymmetrically encrypted and unknowable to me or anyone other than the password holder.
So, if you’re super concerned with privacy, and people signing up have already done this, you can use a temp or anonymous email to sign up for early access and another email to create your account.
The reason I don’t asymmetrically encrypt the early access sign up email, is that there’d be no way for me to email in the future when Early Access is ready to launch. At least, as I’ve designed the system for better or worse. Once Early Access is over I am going to delete all of that invite and email sign up data and it’ll be gone for good.
On Logs
Yes, no personal data is in logs at all. My logs would be frowned upon by probably every operations teams because of how basic, limited, and sparse they are.
It’s just the basic server functioning logs. I don’t personally log anything at this point. This opens up questions about denial of service attacks etc but I just haven’t got there yet. Maybe I will have to do something to address that but we’ll see.
Yes, Render’s privacy policy didn’t have me thrilled but I also felt like I protected against it all with my lack of identifying logs and encryption practices.
Now, they probably have my data for the account with them, but I have to make trade offs myself until a future where maybe I can build out our own infrastructure.
Also, I have a blog post on how I use the session rather than the IP to rate limit log in attempts while preserving privacy. So, I always try to look for solutions like that. That way I don’t have to take someone’s IP which could potentially be very privacy invading.
On Trust
At the end of the day, it all comes down to trust. I’ve learned that you could have a system that end-to-end or asymmetrically encrypts or zero-knowledges everything and still be stealing everyone’s data secretly. You would just do it before the data actually gets encrypted.
Take Zoom for example. They’re currently settling a multi-million dollar lawsuit that essentially shows that they lied about so many things and their settlement lets them claim they did nothing wrong, etc. I find a company like that very difficult to trust (and part of why I decided to make a feature like Portals – which will eventually be super awesome once I get my hands on that WebRTC book coming out in November).
Trust is also essential to a democracy and healthy society. This is another aspect why surveillance capitalism is so destructive to democracy and our societies. Its nature obliterates trust.
I mean even if you open-sourced your code, you could have another code base that you actually use. Again, this is an endless rabbit hole and at the end of the day you have to trust someone at some point. That being said, it’s important that your trust is earned. And in a healthy society trust is continually tested and reaffirmed.
I actually plan to open source Metamorphic after it’s in a more stable and secure position. I think my plan is to hopefully work with another company, like Dashbit, to help me make sure I do everything as good as I can.
To Conclude
Sorry, this is so long. I think I’m now losing my focus. Hope I answered some of your thoughts and concerns. I have put a lot of thought into this, and continue to, and my whole goal is to provide the power of technology to work for people (in this case to connect and share) to make their lives better rather than exploit them.
I don’t think I realized what I set out to do, how actually challenging it would be, but Elixir and Phoenix really make it possible for me.
This would probably make for an easier to follow discussion on a podcast  as it is so much to read.
as it is so much to read.
Perhaps I can invite you to hop on our humble podcast to discuss and learn more about what you’re up to and all of your adventures too? Or someone with a podcast can invite us both on  .
.

 ).
). .
. ).
).